Zero Trust Architecture is a cybersecurity model based on the philosophy of “never trust, always verify.” Every user, device, application, and interaction should be trusted users or devices working on a network in which every access request is continuously validated, authorized, and monitored. Organisations are shifting towards ZTA in order to reduce ransomware risks, secure hybrid workforces, protect Cloud Infrastructure Security, and build compliance across distributed digital infrastructures.
Key Takeaways – At a Glance
- Zero Trust Architecture works on the principle of “never trust, always verify.”
- Traditional Perimeter-based security systems no longer secure organisations for both hybrid and cloud-first security solutions.
- Zero Trust security systems depend on three core pillars, which include identity verification, least-privilege access, and continuous monitoring.
- Successful adoption requires three essential components, which include leadership and organizational culture, and workforce competence.
- Human-centered cybersecurity demonstrates stronger long-term protection capabilities than pure technological security solutions.
Organisations invest in - Zero Trust security to achieve better protection against ransomware attacks, insider threats, and credential-based attacks.
What Is Zero Trust Architecture?
It is a modern cybersecurity framework where no user, device, application, or network should be trusted automatically. Every interaction needs to identity verification, contextual validation, and least-privilege access execution. This process minimizes threat vector and reduces the affect of internal and external cyber threats.
The zta full form in cybersecurity is “Zero Trust Architecture.” It stands as a shift away from perimeter-based security models that were designed for traditional office networks. Those older models pre-assumbe that users inside the corporate firewall are an trusted user.
Remote work, cloud applications, third-party vendors, IoT devices, and hybrid infrastructures have dissolved the traditional network boundary. Attackers now leverage credentials, broken access control, and unregulated cheack points rathern than only attacking firewalls.
That is why zero trust architecture is important and has become a boardroom-level conference rather than only an IT concern.
Source: Zero Threat
Did You Know?
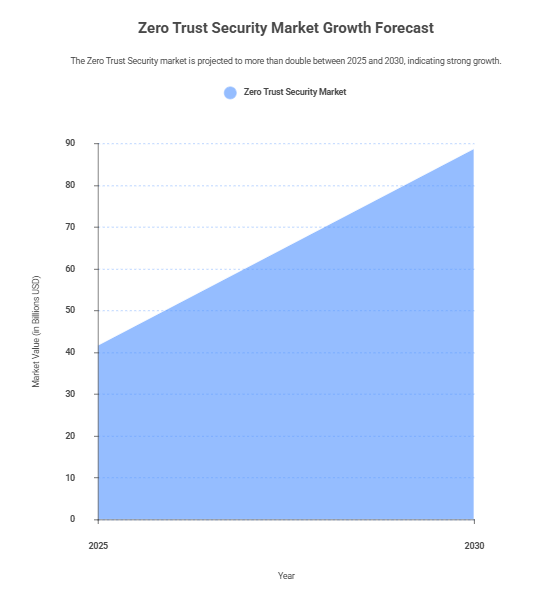
The Zero Trust Security market is expected to increase from USD 41.72 billion in 2025 to USD 88.78 billion in 2030. The market will operate at a compound annual growth rate of 16.3 percent throughout the entire forecast period.
Zero Trust Architecture vs Traditional Architecture: What Has Changed?
The main difference in zero trust architecture vs traditional architecture is that traditional models assume internal trust, while Zero Trust continuously validates every interaction regardless of network location.
| Traditional Security Model | Zero Trust Security Model |
|---|---|
| Trust users inside the network | Verify every request continuously |
| Focus on firewall protection | Focus on identity and access |
| Static authentication | Continuous authentication |
| Broad network access | Least-privilege access |
| Limited visibility | Real-time monitoring and analytics |
| Implicit trust | No implicit trust |
The challenge is clear: once attackers gain enter to a trusted network, they often move sideways with minimal resistance.
In our experience executing security awareness and cyber capability frameworks for financial institutions and Learning Management Systems (LMS) , the largest operational gap is not just about the technology only but it is also about identifying governance and access uthority.
That is where Zero Trust Architecture changes the equation.
Why Are Organisations Shifting Toward Zero Trust Architecture?
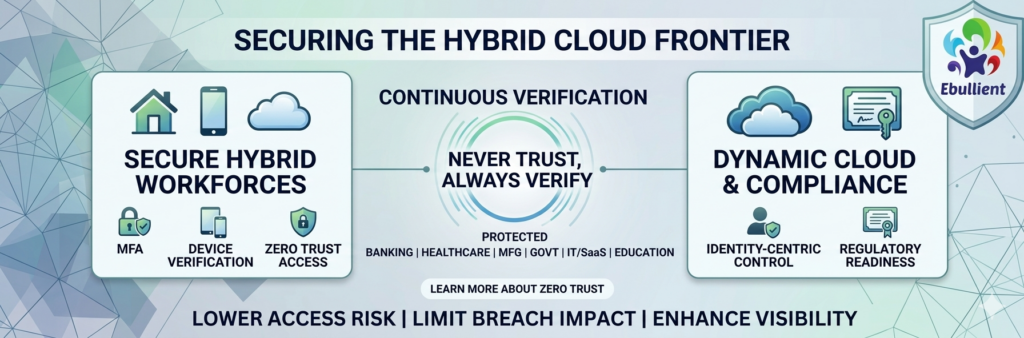
Organisations are moving toward Zero Trust Architecture because cyberattacks progressively target identities, cloud environments, and remote nodes rather than core architecture. Zero Trust lowers unauthorized access, limits breach impact, enhances compliance, and helps in building a secure hybrid work environment.
The shift is happening across industries:
- Banking and financial services
- Healthcare
- Manufacturing
- Government
- IT and SaaS enterprises
- Educational institutions
The Rise of Hybrid Workforces
Remote and hybrid work environments have dramatically expanded attack surfaces.
Employees now access enterprise systems from:
- Home networks
- Personal devices
- Public Wi-Fi
- Cloud applications
- Mobile devices
This decentralization weakens perimeter-based security.
A single compromised credential can expose critical systems unless organisations implement:
- Multi-factor authentication (MFA)
- Device verification
- Role-based access control
- Network segmentation
- Behavioral monitoring
This is one reason that zero-trust architecture, the future of cybersecurity, has become a dominant industry narrative.
Cloud Adoption Is Reshaping Security Models
The process of application deployment and data storage in organizations underwent a transformation through the introduction of cloud computing services.
The conventional models operated under three assumptions:
- The offices of businesses contained all their essential software systems
- Staff members accessed systems through company workspaces
- Network traffic used designated central points for its flow
At the present time:
- Organizations operate their software systems through multiple cloud computing platforms
- Software developers use application programming interfaces to link different software systems
- Workers from any location all over the world
- The business world now uses permanent integration of services from external vendors
- Zero Trust Architecture enables organizations to protect their changing operational environments through identity-based security measures, which replace traditional network security methods.
Regulatory Compliance Pressures
Modern compliance frameworks increasingly expect stronger access controls.
Organizations that operate under these standards:
- PCI DSS
- HIPAA
- GDPR
- ISO 27001
- RBI cybersecurity
- frameworks
- NIST standards
must continuously monitor their systems while managing access to their resources.
The implementation of a mature zero-trust architecture framework enables organisations to achieve the following benefits:
- Audit readiness increases
- Organization operations gain better oversight
- The company can monitor access made by users with special privileges
- The organization can decrease security threats from its own personnel
How Does Zero Trust Architecture Work?
The system conducts ongoing assessments of users’ identities and their devices and the applications they use and all network activities before it permits system access. The Zero Trust Architecture framework restricts system access for users who enter the network because it relies on five security measures which include their identity verification and their device security and their limited access rights and its micro-segmentation capability and its ongoing security surveillance.
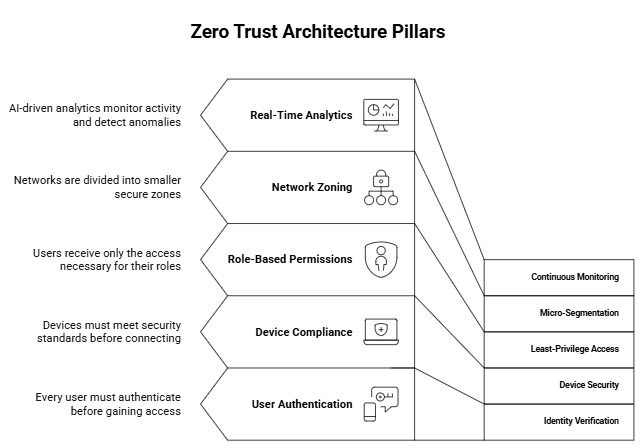
1. Identity Verification
All users need to perform authentication procedures before they can access any system or data. Organizations employ Multi-Factor Authentication (MFA) together with biometric verification and Single Sign-On (SSO) and conditional access policies to enhance their identity protection measures. The Zero Trust Architecture framework establishes identity verification as the new security perimeter.
2. Device Security
The enterprise network requires all devices to undergo security checks before they establish connections with enterprise systems. The security teams assess all devices by reviewing their operating system updates and antivirus status, and their endpoint protection capabilities and device compliance level. The system blocks all access to unmanaged devices and devices showing signs of compromise.
3. Least-Privilege Access
Users receive only the minimum access required for their roles. This security measure helps organizations manage insider threats while preventing users from escalating their access privileges and disclosing confidential information and simultaneously enhancing their overall security controls and governance procedures.
4. Micro-Segmentation
The network infrastructure divides complete networks into multiple secure environments which stop unauthorized users from moving between different network sections. The attackers who breach the first security defense face difficulties when trying to reach vital operational systems and confidential data.
5. Continuous Monitoring
AI-based analytics systems maintain ongoing surveillance of user login activities and file usage behaviors and device operations and security threat detection. The organization uses real-time monitoring to identify suspicious activities more quickly which enables them to respond to cyber threats with greater efficiency.
What Is a Zero Trust Architecture Framework?
A zero trust architecture framework is a systematic cybersecurity model that outlines the policies, technologies, governance processes, and workflows needed to execute the Zero Trust security across an organisation. It supports businesses to continuously verify users, devices, and applications while lowers the unauthorized access and cyber risks.
One of the widely adopted models is the NIST Zero Trust Framework, developed by the National Institute of Standards and Technology (NIST). The framework is developed on key principles such as continuous verification, explicit authentication, least-privilege access, dynamic policy enforcement, and real-time visibility across enterprise systems.
Key Components of a Zero Trust Architecture Framework
| Component | Purpose |
|---|---|
| Identity and Access Management | Authenticate and authorize users |
| Endpoint Security | Secure and validate devices |
| Network Segmentation | Limit lateral movement |
| Data Protection | Protect sensitive information |
| Monitoring and Analytics | Detect suspicious activity |
| Policy Engine | Enforce security decisions |
Why Framework-Based Implementation Matters
Many organizations fail to understand and deploy Zero Trust Architecture as a technology product rather than a long-term security framework. There is not even a single software that can automatically build a Zero Trust environment.
The Successful execution requires:
- Governance alignment
- Strong security culture
- Access control redesign
- Employee cybersecurity training
- Technology integration
This is why enterprise learning, leadership awareness, and cybersecurity capability-building programs play an important role in successful Zero Trust adoption.
Source: Stellar Cyber
Did You Know?
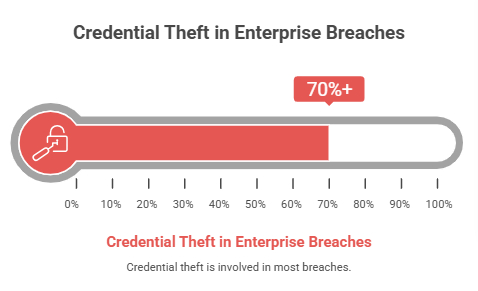
Industry studies estimate that credential theft is involved in over 70% of enterprise breaches. The implementation of continuous authentication, together with least-privilege access, enables organizations to achieve better protection against credential-based attacks.
Why Is Zero Trust Architecture Important for Modern Enterprises?
Why zero trust architecture is important for modern enterprises because as traditional security models are outdated and are not feasible in today’s hybrid, cloud-first, and competative business landscape. Zero Trust Architecture supports organisations lower down the cyber risks, offers secure remote workforces, stronger compliance, and enhance resilience against evolving cyber threats.
Traditional security models were only designed for predictable environments. But modern enterprises operated in BANI conditions — brittle, anxious, nonlinear, and incomprehensible. In this reality, inherent trust becomes a vulnerability.
Zero Trust Architecture allows organisations from assure trust to continuous verification. The system verifies every user and every device and every access request before granting permissions which helps to decrease cyber risks and protect against insider threats and prevent unauthorized access.
Zero Trust security implementation extends beyond technology to protect digital systems which includes:

- Digital trust protection
- Safer hybrid work environments
- Compliance and governance systems
- Adaptive decision-making
- Organizational resilience development
At Ebullient, this intergrates with the belief that technology should amplify human dignity, responsibility, and resilience — not simply automate control. The current cybersecurity transformation process requires organizations to create antifragile systems, which enable them to succeed during uncertainty.
What Is a Real-World Zero Trust Architecture Example?
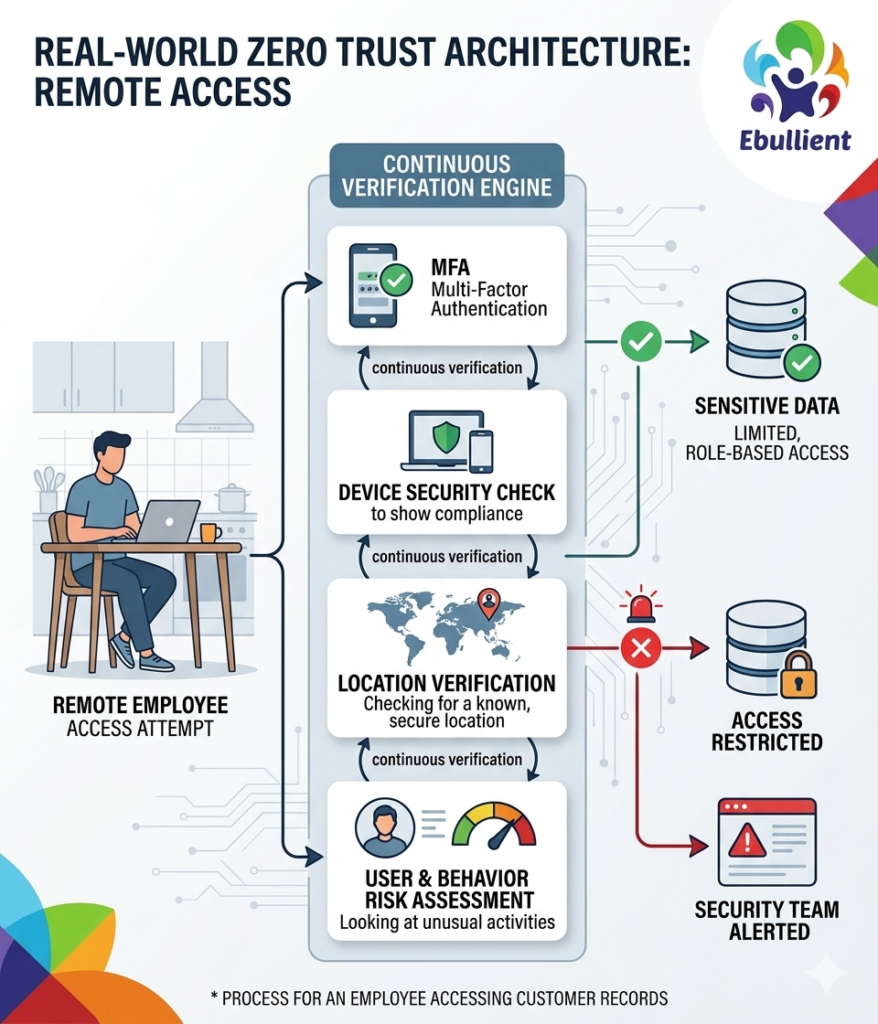
A practical zero trust architecture example is when a remote employee tries to access confidential company data. Before authorizing access, the system consistency verifies the user’s identity, device security, login location, and risk level to make sure for a secure access.
For example, in a financial services organisation, when an employee accesses customer financial records remotely need to first complete Multi-Factor Authentication (MFA). The system then re-checks whether the device is secure and compliant, reviews the login location, and evaluates behavioral activity before authorizing limited access based on the employee’s role.
If suspicious activity is detected, access may be restricted, additional authentication may be activated, and security teams will be immediately alerted. This continuous verification process shows how Zero Trust Architecture works in modern enterprise environments.
What Challenges Do Organisations Face During Zero Trust Implementation?
Organisations deploying Zero Trust Architecture may often face challenges such as employee resistance, legacy systems, weak identity governance, and limited cybersecurity awareness. Since Zero Trust heavily depends on user behavior and access control, technology only cannot prevent risks like credential sharing, weak passwords, phishing attacks, or unauthorized access.
Successful execution needs continuous training for employees:
- MFA best practices
- Identity security
- Secure remote work
- Device hygiene
- Access control protocols
At the leadership level, organisations need to build a stronger governance around risk ownership, vendor access management, and Incident Response Coordination. At Ebullient, we believe cybersecurity transformation succeeds when organisations align technology with cultural rewiring, adaptive leadership, and human-centered capability building.
Why Is Zero Trust Architecture Considered the Future of Cybersecurity?
Experts consider zero trust architecture the future of cybersecurity because it is designed for modern digital environments which emerge from cloud computing and hybrid workforces and AI-powered threats and interconnected systems where traditional perimeter-based security models are no longer effective.
Cyber threats have developed into more sophisticated attacks which now use artificial intelligence for phishing and credential theft and deepfake social engineering and automated attacks. The architectural design of Zero Trust Architecture provides complete protection against security threats through its three core functions which include continuous verification and identity-based access control and real-time system observation.
Organizations face growing security risks because of their increased dependence on third-party vendors and IoT devices and edge technologies. The Zero Trust security model enables organizations to minimize their security threats through restricted system access which allows users to see only their job-related systems and data.
Today, cybersecurity is also a board-level priority. Business leaders now focus on:
- Operational resilience
- Regulatory compliance
- Brand reputation
- Business continuity
How Ebullient Helps Organisations Build Zero Trust Readiness?
Effective cybersecurity requires organisations to develop their systems and processes in addition to implementing technology solutions, according to our organisation.
Ebullient helps organisations to handle their hybrid work challenges together with their AI systems and their growing cybersecurity threats through the following services:
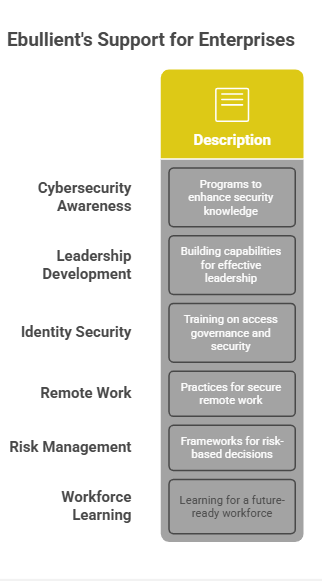
- Cybersecurity awareness programs
- Leadership capability development
- Identity security and access governance training
- Secure remote work practices
- Risk-based decision-making frameworks
- Future-ready workforce learning
Ebullient training approach develop antifragile leadership and responsible digital practices and sustainable organizational cultures which differ from conventional training methods. Our approach aligns technology with human dignity, trust, creativity, and long-term organizational resilience — helping enterprises strengthen both cybersecurity posture and future readiness.
Final Thoughts
Zero Trust Architecture is no longer an emerging concept reserved for highly regulated industries. It has become a strategic necessity for organisations managing hybrid workforces, cloud ecosystems, sensitive customer data, and evolving cyber threats.
The companies that treat cybersecurity as a continuous business capability—not a one-time technology deployment—will be far better positioned to manage future risks.
Frequently Asked Questions
Get answers to commonly asked questions about Ebullient.
Why Are Organisations Rapidly Adopting Zero Trust Architecture in 2026?
What is Zero Trust Architecture?
The cybersecurity framework operates by needing to authenticate all user, device, and system connection attempts before it will allow users to access organizational resources.
How does Zero Trust Architecture work?
The system establishes user identity through identification methods, it maintains restricted access through least-privilege permissions, and performs ongoing system checks to identify user behavior patterns and implement security measures through dynamic protection methods.
Why is Zero Trust Architecture important?
The traditional trust model fails to meet modern requirements because organizations now function in environments that use distributed systems and cloud technologies and maintain constant connections with other systems.
What industries benefit most from Zero Trust?
The financial services sector, along with healthcare and government, manufacturing, educational institutions and technology industries, all experience major advantages because they handle confidential information and operate extensive digital systems.
Is employee training necessary for Zero Trust implementation?
Yes. The success of Zero Trust requires organizations to develop their workforce capabilities because employee behavior determines authentication methods and credential protection and the ability to resist phishing attempts and access control systems.



